A fundamental problem with biometric authentication
Wouldn’t it be great if you could just sit down at your computer and have it recognize you? Remembering usernames and passwords to authenticate you to various computer resources can be quite a pain.
 IT help desks across the world see a constant stream of password reset requests due to forgotten passwords, but this is precisely the appeal that password authentication has over biometric authentication. You can change your password and hold a multitude of different user accounts without necessarily revealing your identity.
IT help desks across the world see a constant stream of password reset requests due to forgotten passwords, but this is precisely the appeal that password authentication has over biometric authentication. You can change your password and hold a multitude of different user accounts without necessarily revealing your identity.
Biometrics, meaning measurements (metrics) of the biology (you)– fingerprint, iris, retina, face recognition, voice recognition, brain wave, DNA, or any number of features that are unique to individuals, can be used for identification. Biometric authentication has one fatal security flaw however that prevents using it in high security systems: Individuals can’t change their biometrics. Once an attacker gets your fingerprint, iris, retina scan, voice print or other hash in a standardized format, they can use it to impersonate you.
Here are some ways biometric authentication can be defeated, unless used in conjunction with a password. This is obviously for informational purposes only, as a security assessment of these technologies. I don’t recommend you do any of these things.
Fingerprint readers [Difficulty: moderate]
Pull someone’s fingerprint off a used beverage glass or can. CNC machine or create a photoresist mold of said fingerprint from a scan of the print, or from a fingerprint hash obtained from an existing authentication database. Cast it in silicone. Attacker wears the cast over her fingertip, spoofing the victim’s print.
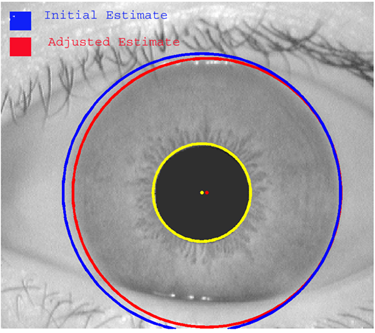
Iris scanners [Difficulty: moderate]
Shoot a high res photo of someone’s iris or obtain the raw biometric hash from an existing system. Create a contact lens with this image printed on it.
Retina scanners [Difficulty: hard]
Because the retina is on the back of the eye, it’s not something that could be easily “skimmed” in public. In the sci-fi novel Snow Crash (Neal Stephenson), there were laser iris scanners that could scan an iris from a distance. Even though that technology doesn’t exist yet, one could use an existing hash of the retina scan to create a combination contact lens with a hologram of the retina and the victim’s iris print built into one. This holographic technology already exists and is only getting cheaper.
Voice print [Difficulty: moderate]
Voice print authentications systems use various algorithms to match a user’s voice to a known “voice print” hash or pre-recorded phrase. A shotgun microphone can remotely record the sound of a person logging in, or phrases can be pieced together using phonemes (short sounds) taken from pre-recorded samples of the victim’s voice. The voice can be played back over a speaker to the authentication system. There are two-factor voice print systems that ask the user to read a dynamically generated word, but again using sample based techniques, it’s possible to synthesize a person’s voice dynamically.
DNA reader [Difficulty: hard]
The only way one could defeat current DNA sequencing technology would be by stealing some tissue (or pre-cloning it) from the victim, which would be used to spoof their identity. DNA sequencing is too slow and expensive to be used for authentication currently, however recent microfluidic lab-on-chip technologies have provided dramatic speed increases.
In any of these systems, if it’s physically accessible, one can bypass the scanner input subsystem and pass the raw, forged sensor data to the host software. If one already has the hash data from an existing database, no snooping or device fabrication is required.
Let’s just keep one thing in mind about biometrics. We’re talking about identification, not authentication. If, as a society, we ever decide to rely solely on biometrics for authentication, we will have an epidemic of identity theft. You can easily come up with a new password, completely independent of your identity. There’s no practical way to change your biometric data.
Say we live in a society that relies on biometrics for authentication to sensitive resources, and a criminal does actually steal your biometric data, they could wreak absolute havoc in your life. Since you can’t change it, more and more criminals could use your identity as your biometric hash spreads thru the underground networks, the way social security numbers do today.
Let me tell you, identity theft is real. I once got a phone bill for over $1000 due to identity theft. Took me 6 months to clear that mess up. Passwords are a pain but a strong password is the only thing standing between you and having your phone disconnected over fraudulent charges.
Also if you don’t have one, you should get a paper shredder.
47 Responses to “A fundamental problem with biometric authentication”
-
Plus Biometric is pretty useless for remote authentication as you can’t tell if the scanner has been compromised letting people just send captured biometric data with out the trouble of making prosthetic finger tips, contact lenses, etc.
thinking about the hash thing if you can compromise the scanner you could use the end result of one-way hash as that is presumably what is been sent from the scanner.
Leave a Reply
You must be logged in to post a comment.



 NoScript extension
NoScript extension
